Blog
July 26, 2022
As a developer or DevOps tester, you can store APIs on AWS on the Amazon API Gateway. But it is important to know that when you load test these APIs, your testing script has to include the AWS Signature, which are its access credentials.
This blog post will explain how to add the AWS SigV4 signature to your Apache JMeter™ test in Groovy, so you can successfully run API functional and load tests. Let’s get started.
Table of Contents:
Back to topWhat is AWS SigV4?
Signature Version 4 is the current AWS signing protocol, and is used to authenticate information to HTTP AWS requests. AWS signatures consist of an access key ID and secret access key. They are used for identifying who sent requests and for protecting data.
You can also learn how Signature Version 4 works from the AWS documentation.
Back to topUsing AWS SigV4 in JMeter
JMeter is a popular open source load testing tool that enables teams to test multiple scenarios and use cases. With AWS’s popularity, it is important to understand how to include its configurations in your load test, so you can simulate your real user behavior. Let’s see how it’s done.
Creating Your JMeter Test
Our JMeter test will send an HTTP request to an AWS API. We will use a Groovy script in a JSR223 PreProcessor to generate the AWS Signature and then use a Regular HTTP Request to call the API.
Prerequisites
Before you start testing, you need to download the following JAR files and add them to JMeter:
Our Load / Functional Testing Script
1. Add a Thread Group
Add -> Threads -> Thread Group
2. Add User Defined Variables as a child element of the Thread Group.
Thread Group -> Config Element -> User Defined Variables
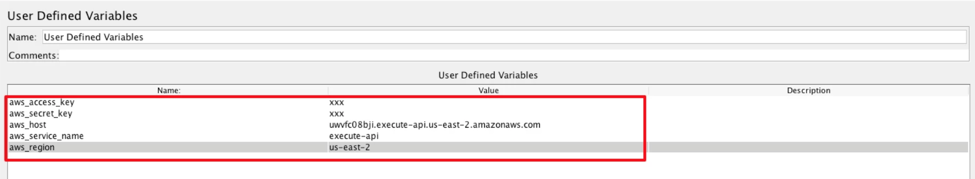
3. Complete the missing values for your User Defined Variables. Add the AWS access key, secret key, host, service name and region. You should obtain these from your Amazon account.
4. Add a JSR223 PreProcessor to your Thread Group.
Thread Group -> Add -> Pre Processors -> JSR223 PreProcessor
In this scenario, the PreProcessor will use Groovy, a very flexible language for adding a PreProcessor to a thread group.
5. Add your code to the PreProcessor you just added. This code is configured to create two JMeter variables with the AWS signature, which will be used to let you call your API in AWS (get the code example).
You can add the code as is, without having to change a single thing.
The code:
- Gets the values from the user defined variables.
- Gets the values from the HTTP Sampler we will configure in the next step.
- Generates an AWS Date, which Amazon requires when calling the API.
- Creates a JMeter variable with the date stored in it.
- Calculates the AWS signature.
- Creates a JMeter variable with an AWS authorization header.
These two variables can now be used to call the API on AWS and test it.
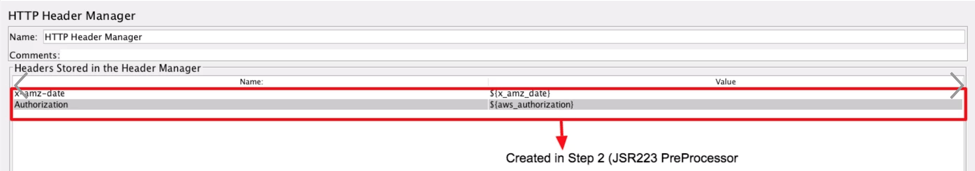
6. Add a HTTP Header Manager to the Test Plan
Test Plan -> Add -> Config Element -> HTTP Header Manager
The header is required by Amazon to call the APIs.
7. Add Header names: x-amz-date (for the AWS Date) with the value ${x_amz_date}, and Authorization (for the AWS signature) with the value ${aws_authorization}.
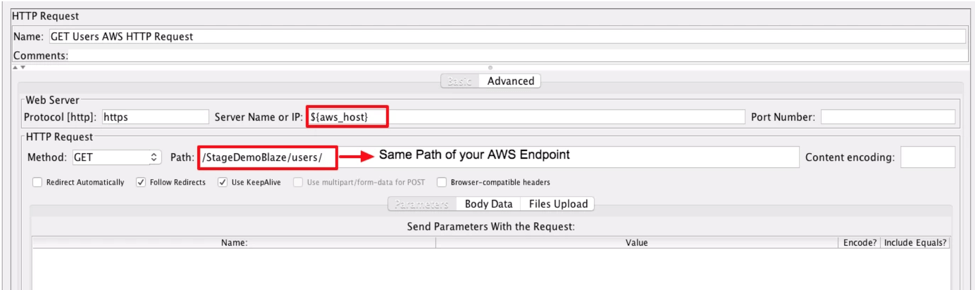
8. Add an HTTP Request Sampler (as many as you want). These are for calling the API endpoints.
The server name has to be ${aws_host} and the path should be the same path of your AWS endpoint.
Specify the method and body according to your scenario.
9. Consider adding a Cookie Manager, an HTTP Cache Manager and Timers in your script to improve the CPU of your test.
Your script is ready to run!
10. Add a Listener and run your test.
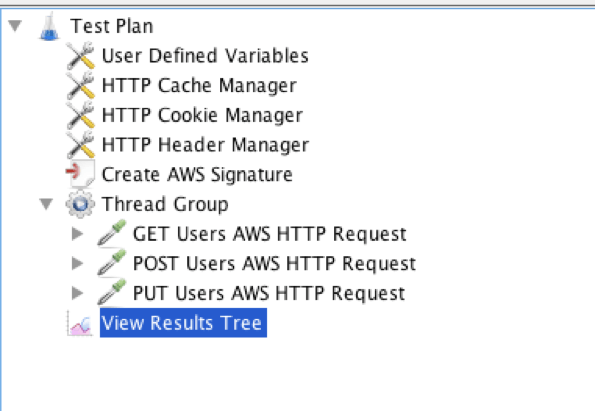
Check to make sure you included all of the necessary steps. This is what the full test script should look like:
Back to topBottom Line
That’s it! You now know how to add an AWS SigV4 signature to your JMeter tests.
Now, you can also take your JMeter script in BlazeMeter and run it in the cloud or behind a firewall. You can scale your test, run from multiple locations, and get advanced reports for better collaboration.
Explore JMeter testing in action, and try out BlazeMeter today.